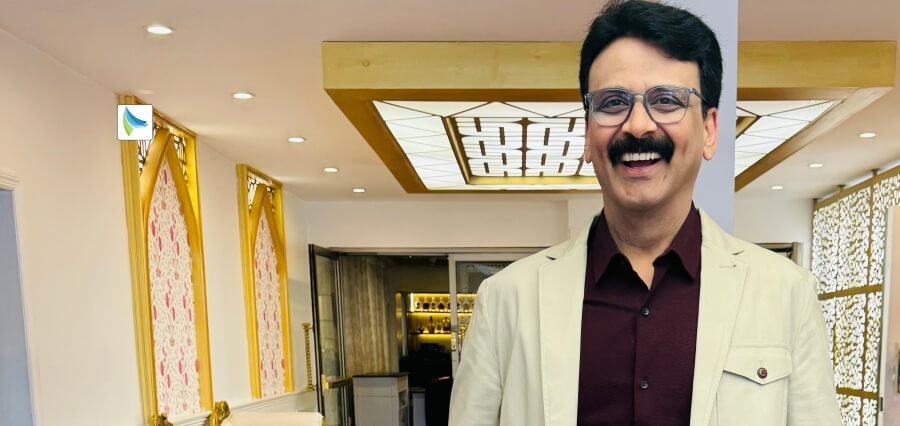
The intricate landscape of cybersecurity demands a leader with a wealth of experience and a strategic vision. Howard Zach, the seasoned President of Digital Beachhead, Inc., stands out as the leader dedicated to excellence in this landscape. With a comprehensive portfolio overseeing operations in the US and Canada, Howard brings expertise cultivated over a remarkable career. His journey includes a pivotal role as the Vice President of Enterprise IT Services at CRGT, where he managed a $60M/year business, spanning diverse customers across the Federal space in seven countries.
Howard’s journey is marked by proficiency in business development, having served in key positions at CRGT and as Director and VP of Business Development at CiBER Federal, Inc. before its merger with CRGT. Before diving into the cybersecurity realm, Howard navigated challenging program management roles with industry giants Boeing, L-3 Communications and Computer Sciences Corporation.
Notably, Howard is not just a corporate leader—he is a seven-year veteran of the US Navy and boasts 15 years of Federal Service. His multifaceted background, coupled with a dedication to distinction, positions Howard as a key player in the dynamic world of cybersecurity at Digital Beachhead.
Let’s explore how Howard is driving Digital Beachhead towards unparalleled success!
Passion, Challenges and Cybersecurity
Howard’s journey into the cybersecurity realm began in the Navy, where he cultivated a profound understanding of balancing security and service. As a federal contractor, he spearheaded diverse technical teams, navigating through complex, enterprise-wide challenges, notably focusing on network security. In his words, “I have a passion for technology and new challenges—cybersecurity provides both of these in spades.”
Howard’s dedication extends to collaborating with clients, ethically resolving issues and navigating the ever-changing landscape of cybersecurity. His journey underscores the search for surety and security in the cyber domain. For Howard, the allure lies in the dynamic intersection of technology, challenges and ethical solutions making cybersecurity a compelling and ever-evolving pursuit for enthusiasts and professionals alike.
Legislative Labyrinth
Navigating the cybersecurity landscape entails confronting dual challenges, as Howard eloquently puts it, “The challenges are two-fold.” The first hurdle involves ensuring service consistency across jurisdictions amid the ever-evolving legislative landscape. In the U.S., the focus is predominantly at the State level, whereas in Canada there’s a historical federal inclination that has recently shifted to a provincial emphasis. The crux lies in the necessity for legislators in both countries to safeguard data privacy and business operations leading to a varied panorama of legislation at the State-by-State and Province-by-Province level.
Howard sheds light on the complexity, stating that it becomes a very mixed picture regarding the scope of the legislation measurements and means of measuring cybersecurity solutions as well as results, reporting responsibilities and penalties assessed for violations and
non-compliance. The second challenge magnifies as a persistent struggle: the scarcity of skilled cybersecurity professionals.
Howard underscores the dilemma, expressing that the current demand for experts has outstripped the supply. While educational institutions are responding with cybersecurity programs, transitioning eager beginners into proficient cybersecurity teams is a gradual process. Howard’s insights encapsulate the complex combination of legislative intricacies and the pressing need for a skilled cybersecurity workforce, making this a relevant and engaging topic for readers across diverse backgrounds.
Unraveling the Complexities
Howard’s journey has endowed him with a profound understanding of the national systems, supply chain vulnerabilities and data privacy concerns. In his words, “I came to recognize that cybersecurity addresses a critical need faced by individuals, businesses and the government.” The core issue lies in mitigating dependencies on third-party entities, a potential source of vulnerability. His experiences have emphasized the complexity of securing the entire supply chain acknowledging the inherent difficulty in exercising control.
“Cybersecurity works to give businesses the ability to gauge and establish the level of risk they are willing to accept,” Howard emphasizes. Amid a myriad of technical solutions, Digital Beachhead stands out by prioritizing customer rapport over a one-size-fits-all approach. As Howard aptly puts it, “We believe the path to cybersecurity begins with a conversation.”
The focus extends beyond mere checkbox solutions recognizing the imperative to balance security with operational and business outcomes. This approach underscores a commitment to understanding client needs and tailoring solutions accordingly. Howard’s insights focus on the nuanced landscape of cybersecurity emphasizing the importance of dialogue in forging a secure path for individuals, businesses and government entities alike.
Market Mastery
Howard acknowledges that the biggest challenge is always in understanding the market. His approach revolves around a multi-phased strategy grounded in comprehending customer imperatives and organizational goals. With a focus on innovation, threat landscapes, user-centric security, and collaboration, Howard delves into a meticulous process.
To begin, he stresses the importance of understanding the marketplace from the perspective of the potential customer base. This entails a deep dive into products, services, technology, customer bases, and the supporting supply chain. Howard meticulously evaluates these elements to formulate a top-level list of potential markets and customers, considering their potential value to Digital Beachhead. Subsequently, he crafts a nuanced go-to-market strategy.
Howard underscores the iterative nature of this process, stating, “We have to review the results and the analysis consistently.” The key is to ensure accuracy and adapt the focus based on insights gained from market interactions. This strategic approach illuminates the significance of understanding and adapting to the dynamic market landscape, a crucial insight applicable to a diverse readership.
Learning from Mistakes
Howard highlights a crucial advantage due to seven-year tenure in the US Navy and 15 years of Federal Service by stating, “The greatest advantage I’ve found is knowing the importance of leading by example and being willing to make a decision.” In the realm of cybersecurity, where complexities abound, this involves not just managing but leading. Howard emphasizes the significance of having a vision and leading the exploration of new technologies to stay ahead of emerging threats.
Empowering and trusting his staff is a core principle for Howard, who believes in teaching them to make decisions and take ownership of their work. Recognizing the inevitability of mistakes, Howard fosters a culture that values learning from errors, stating, “It’s okay to make a mistake as long as we learn from it.” He underscores the critical role of team autonomy and sets clear expectations for corporate success in the dynamic field of cybersecurity.
In Howard’s perspective, Cybersecurity ultimately focuses on risk management, necessitating independent, knowledgeable and confident staff who can support customers effectively. This, Howard asserts, is only achievable through empowerment—a key to success in the landscape of cybersecurity.
Strategic Security
Howard zeroes in on the prevailing challenges in the cybersecurity landscape, noting, “We see the primary challenges faced by our customers and the market we serve in the sophistication of the cyber threats.” With a surge in ransomware attacks and the belated identification of supply chain vulnerabilities, Digital Beachhead (DBH) is committed to addressing these issues head-on.
DBH recognizes the imperative to assist customers in honing a security posture that mitigates risks and reduces the likelihood of cyber-attacks. Howard explains, “We work with our customers to establish actionable cybersecurity policies and procedures, establish consistent training and testing of our customers’ employees.” Additionally, DBH focuses on the implementation of security and end-point monitoring, ensuring customers are well-informed and comfortable with proactive responses to anomalies.
Crucially, Howard emphasizes the balanced approach, aligning security measures with customer preferences and risk acceptance that aligns with their corporate affordability goals. This holistic strategy positions DBH as a proactive partner in navigating the intricate landscape of cybersecurity addressing both immediate threats and long-term security postures.
Vision, Collaboration and Experimentation
Howard underscores the importance of vision, stating, “I mentioned vision earlier and that’s a critical ingredient to our corporate success.” However, he adds a crucial nuance—success is achievable only when vision is coupled with encouraging collaboration and creating a space for experimentation.
At DBH, Howard emphasizes consistent effort in working within cross-functional teams. This approach is designed to maximize employees’ diverse perspectives, capabilities and backgrounds as well as experience. The goal is clear—to collaboratively solve complex problems, whether it’s evaluating zero-trust architectures and solutions or delving into potential threats posed by AI and Machine Learning.
This commitment to collaboration and experimentation positions DBH at the forefront of innovative problem-solving in the dynamic landscape of cybersecurity.
Adapt, Respect, Succeed
Howard delves into the significance of cultural intelligence, noting, “It starts with cultural intelligence and required me to learn about the different cultures, values, communication styles, and expectations in each country and people group.” The crux, he emphasizes, is adaptability, especially in managing the multicultural aspects integral to operations in both the US and Canada.
“While there are great similarities in language,” Howard points out, “there are different and distinct cultural considerations and festivals.” Recognizing the importance of these nuances, DBH tailors its operating model to each country’s unique environment and cultural dynamics respecting the significance of local customs and celebrations to employees and customers alike.
Howard’s final emphasis underscores the overarching importance of inclusivity and diversity in the workplace. This commitment stems from both personal and corporate values, placing utmost importance on respecting cultural differences that can subtly impact even the simplest of conversations. The holistic approach to cultural understanding and inclusivity at DBH serves as a cornerstone for successful and respectful operations.
Prototyping Excellence
At DBH, the commitment to staying ahead in the cybersecurity landscape is staunch, as Howard notes, “DBH consistently scouts and analyzes the cybersecurity landscape to identify emerging threats, trends and technological advancements.” This proactive approach demands continuous engagement with academic research, industry reports and innovations across AI, machine learning, blockchain, quantum computing, and IoT security.
Collaboration is key and Howard emphasizes, “We foster collaborations with academia, research institutions, industry peers, and government agencies.” These partnerships serve as vital conduits for exchanging ideas, resources and expertise. DBH goes a step further by developing prototypes and subjecting them to rigorous testing.
Howard underscores this rigorous process, stating, “DBH also develops prototypes for potential solutions and conducts rigorous testing of new security solutions, algorithms, and/or tools before recommending them to a client.” This meticulous approach ensures that clients benefit from thoroughly vetted and cutting-edge cybersecurity solutions.
Succeeding Today, Planning for Tomorrow
Howard’s leadership philosophy revolves around preparing successors for success, as he believes, “My role as a leader is to prepare my replacement to take my position and be even more successful.” This forward-looking approach shapes the vision at DBH, where employees collaboratively work towards securing digital ecosystems and becoming a trusted partner in the market.
The emphasis is on enabling innovation and reliable solutions that are resilient and adaptive to evolving threats. Howard underscores DBH’s commitment to being a customer-centric partner, understanding and addressing their needs and goals.
Importantly, ethical cybersecurity practices are at the core, promoting transparency, accountability and responsible vulnerability disclosure.
Howard’s advocacy for consistent and ethical practices not only guides DBH’s internal operations but also resonates as a message to customers. It underscores a commitment to building trust and ensuring the safeguarding of digital assets and individual privacy.
Strategic Specialization
Howard’s advice for aspiring cybersecurity professionals is distinct, “I want to encourage aspiring professionals to find their niche within cybersecurity and make it their specialization.” While acknowledging the need for a broad knowledge base, he emphasizes the criticality of specialization in disciplines like penetration testing, cloud security, or compliance.
In Howard’s words, “Each domain has very different challenges, specific rules, roles, and requirements while also providing a strong foundation that would serve as a very solid base for a cybersecurity career.” For newcomers, he recommends focusing on two rapidly growing areas—cloud security and Internet of Things (IoT) security. These domains represent a significant potential job opportunity for decades.
For those venturing into cloud security, Howard highlights the necessity of expertise in data protection, encryption and identity/access control management. On the other hand, IoT cybersecurity professionals should concentrate on device security, robust credentialing, encryption, network segmentation, and securing the supply chain. Howard’s insights offer a strategic roadmap for aspiring professionals, guiding them to carve out a specialized and impactful niche in the dynamic field of cybersecurity.