The complexities that come with today’s increased digitization are ever-apparent, and the risk of cyber-attacks is growing exponentially. Recognizing this, Boston based CyberSaint Security, a leading cyber-security software firm, helps organizations manage cyber-security risks through its flagship CyberStrong integrated risk management (IRM) platform. The platform was built by a team whose intellectual DNA winds deeply through the academic, tech and investment communities in Boston, the White House, RSA, IBM, EMC, KPMG, MIT, Harvard and others. CyberSaint’s mission is to empower organizations to manage cyber-security as a business function through the adoption of powerful technology that enables measurement, enhances communication and improves cyber-security resiliency.
The CyberStrong Platform is an integrated risk management solution powering automated, intelligent cyber-security compliance and risk management. Built on the gold-standard foundation of the NIST Cyber-security Framework, CyberStrong’s capabilities streamline GRC activities and provide a single pane of glass through which CISOs and their security teams can measure, report, and mitigate risk. CyberStrong’s unparalleled time-to-value, breakthrough Artificial Intelligence and Machine Learning automation eliminate manual effort and help organizations make informed decisions that reduce risk while driving overall business value.
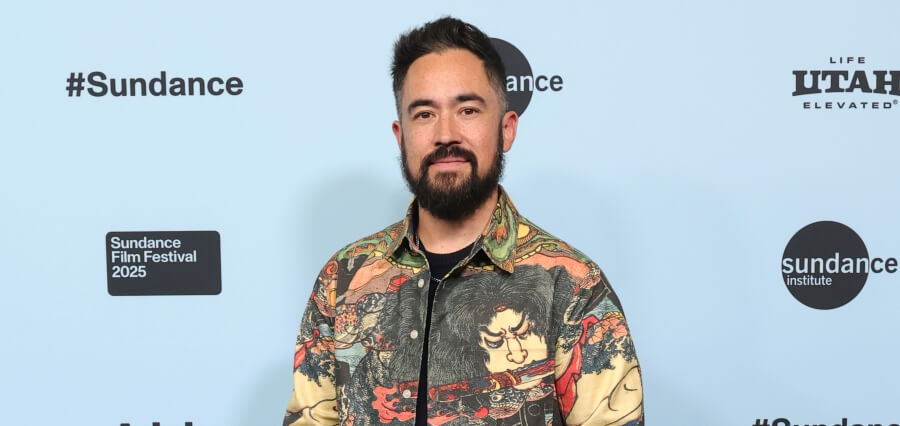
Fortune 500 CSO turned CEO
George Wrenn is the founder and CEO of CyberSaint Security, exhibiting over 20+ years of comprehensive experience. Prior to his current role, he was the CSO and VP of Cyber-security for Schneider Electric, a Fortune 500 global power company. Prior, George was a senior managing consultant with IBM, helping cross-industry Fortune 1000 customers reach compliance to NIST, FISMA, ISO/IEC, HIPAA, PCI, NERC/CIP, and other key regulatory frameworks, developing cyber security strategy, roadmaps, and global cyber security programs. Till date, he has collaborated, reviewed, and added value in the development of frameworks and standards such as the NIST Cyber-security Framework and others.
George is a graduate from Harvard University and has attended executive programs at Harvard Business School and the Harvard Kennedy School. As a Graduate Fellow at MIT for over a decade, he conducts research and advanced coursework at the MIT Media Lab, the Sloan School of Management, the School of Engineering, the School of Architecture and most recently the MIT Security Studies program working on Cyber Warfare frameworks. He is also an Affiliate and Researcher at MIT’s Executive Development program specializing in the NIST Cyber-security Framework.
George is a seasoned keynote speaker, and has spoken at the inaugural NIST Cyber-security Risk Management Conference on IoT Security and Digital Risk Management. He has also had an NSA sponsored ISSEP credential, a Certified Ethical Hacker and CISSP for more than 12 years. George has experience working with the complex Cloud, Government, IT, ICS, audit and national regulatory frameworks. He was also a mission oriented Operations Officer and SAR/DR Pilot (Officer 1st Lt. USAF/Aux) where he served as 1st lieutenant, and has received a National Commander’s Commendation Award for outstanding duty performance with the Hanscom Composite Squadron (HCS-MA-043) based at Hanscom Air Force Base.
Automating GRC to Fuel an Integrated Approach
The CyberStrong platform automates the manual assessment processes that deter organizations from rapid adoption of gold standards such as the NIST CSF. The platform supports ISO27001/2, GDPR, COBIT, IEC62443, and any other framework- including custom controls and hybrid frameworks. CyberStrong’s proprietary control optimization uses patented machine learning and artificial intelligence for faster risk management decision making and automated risk mitigation action planning. CyberStrong ingests its client’s assessment data to provide risk quantification and analytics that identify their current gaps, and maps this data across people, process, technology, risk, and cost to provide an optimization that identifies low-hanging- fruit opportunities to mitigate risk for the lowest cost and highest impact on their posture.
This patented optimization encourages ‘always-on’ continuous improvement, and is completely automated in real-time, requiring zero manual effort to produce fully customized mitigation plans. In addition, CyberStrong’s integrated threat feed automates the prioritization of controls for remediation based on real-time detection of threats that appear active at any time, for any assessment.
CyberSaint believes that by 2020, 100% of large enterprises will be asked to report to their Board of Directors on cyber-security and technology risk at least annually, which is an increase from today’s 40%. According to Gartner, as enterprise stakeholders take an increasing interest and concern about the security posture, the CISO needs to be able to convey their activities and success as effectively as a CFO can with a balance sheet and statement of cash flows.
This approach will ensure that all leaders, in every department regardless of security expertise, can understand the enterprise’s risk posture, what affects it, and what to be aware of. There are four recommended reports necessary to help you align your activities as a CISO with the goals and objectives of the enterprise: Executive Risk Report, Trend Report, GDPR Report, and Global Report – all which are automated from within the CyberStrong interface with no human effort required. CyberStrong allows CISOs to effectively communicate their strategies in a way that is universally understood.
Client Feedback
“CyberStrong provides me with a means to effectively measure and communicate our overall compliance posture, AI to model my security investments for the best ROI, and information on risk exposure using an industry standard model paired with innovative technology. Bright Horizons management can now evaluate clear gaps and work with my team to manage risk across the enterprise.” Javed Ikbal, CISO and VP of Information Security, Risk Management & Compliance at Bright Horizons Family Solutions (NYSE: BFAM)
“CyberStrong provides an easy-to-use platform for us to maintain our compliance with the new DoD DFARS regulation. The team from CyberSaint got us up and running very quickly and now we manage our DoD compliance on our own.” Anthony Santagati, CFO at Senior (Senior Plc- LSE: SNR) Aerospace Metal Bellows.